How to Detect SYN Flood Attacks with Capsa
Denial-of-service attack (DoS attack) is a malicious attack to make a machine or network resource unavailable to users, usually by temporarily or indefinitely disrupting services of a host connected to the Internet. (US-CERT 2013)
Today, DoS attack is a common cyber-attack on the network. According to the statistics, every three seconds, there is a DoS attack happened on the Internet. The low cost of launching a DoS attack is one of the major causes of frequent DoS attacks.
Some of the most commonly used DoS attack types include:
Ping of Death, Teardrop, WinNuk, UDP flood, TCP SYN flood, IP Spoofing, Land Attack, Smurf, ICMP flood, etc.
In this article, we will show you how to detect SYN flood attacks using a network analyzer such as Colasoft Capsa.
In order to analyze DoS attacks, we need to follow three steps below.
Observation
Most of hosts which are under DoS attack will show high CPU and memory usage or network bandwidth is occupied by garbage traffic.
Analysis
We can analyze and locate the attacks by decoding the raw packets. In this way, we will get protocols and behaviors of packets. Compare this information with attack signature, then we can locate the attacks.
Locate issues
With TCP/UDP session and chart function, we are able to locate DOS attacks more accurately and quickly.
Next, I will give you an example to show you the detailed steps.
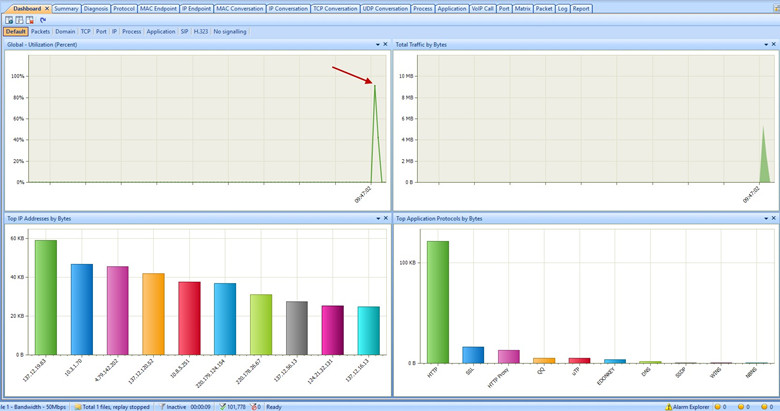
The Dashboard view dynamically displays statistics with various charts. In Dashboard view, the first graph definitely points out our network has the anomaly traffic. Because the utilization of our network almost reached to 100%. Then, go to Summary view to check summary data statistics.
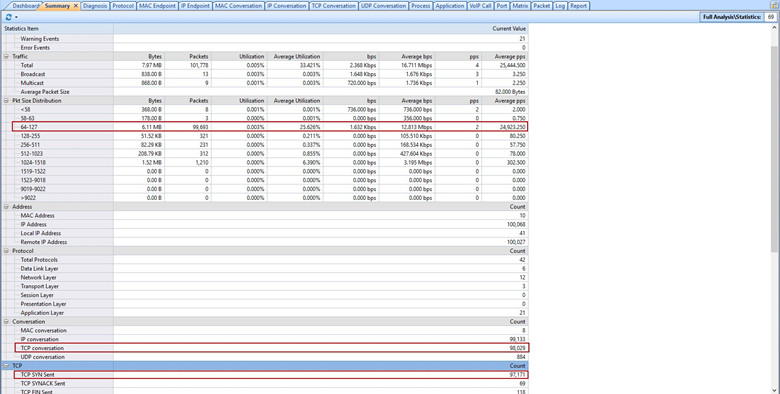
Under the Summary view, summary statistics of current capture are displayed. According to these statistics, we can find out there are too many small size packets in the network. In addition, the count of TCP conversations and TCP SYN sent packets are abnormal.
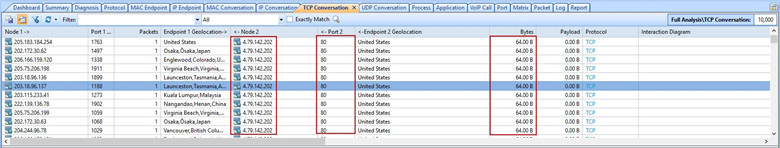
Then, go to TCP Conversation view to check up abnormal TCP conversations. From this view, we are able to see this IP address “4.79.142.202” received a lot of packets from random Internet IP addresses. All these random Internet IP addresses sent the same 64 bytes packet to 80 port on the host “4.79.142.202”.
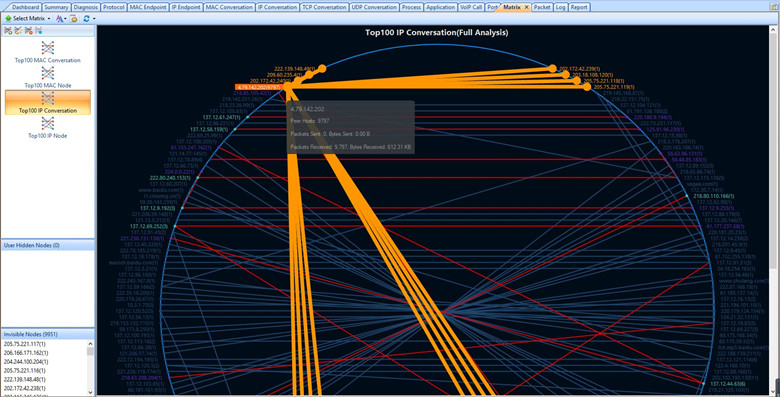
Besides, with Matrix view, it shows that almost 10,000 hosts have conversations with the host “4.79.142.202”.
Last, by decoding TCP packets, we can see the Time Sequence diagram of TCP conversations. The host “4.79.142.202” received repeated SYN packets from different Internet IP addresses. But TCP three-way handshake didn’t establish normally in every TCP conversation.
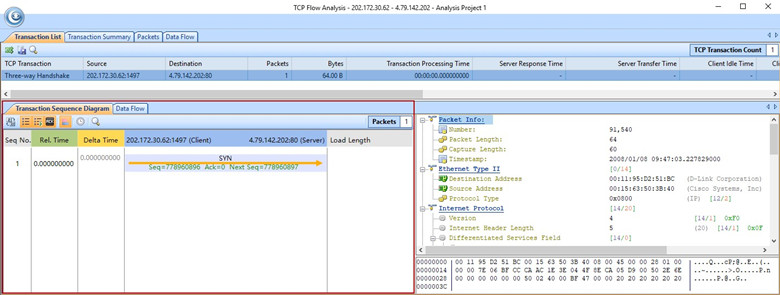
Combine with the above information, we can identify that there are SYN Flood Attacks happened in our network. And IP address of the targeted server is “4.79.142.202”. Because of the attack, it caused the abnormal traffic and consumed our network resources.
Thanks for reading this articls. If you want to get more information about Capsa. Please click here to see more about itYou may also like those articles:
How to Detect Routing Loops and Physical Loops
IT departments are often faced dealing with network loops and broadcast storms that are caused by user error, faulty network devices...
How to Detect Arp Attacks & Arp Flooding
During ARP attacks, users usually experience slow communication on the network and especially when communicating with the host...
How to Monitor http Traffic with Packet Sniffer
In order to monitor http traffic, we will need a packet sniffer (or a protocol analyzer) software. Here is a detail process how we can monitor...
Monitor Network Traffic
As a network analyzer (aka. packet sniffer & protocol analyzer), Capsa makes it easy to monitor and analyze network traffic in its intuitive...
How to use VoIP Analysis
Capsa provides a VoIP analysis module to capture and analyze VoIP calls and graphically display VoIP analysis results, which helps IT...
What is HTTP Sniffer
HTTP Sniffer is a HTTP packet sniffer, protocol analyzer and file reassembly software based on windows platform. Unlike most other sniffers...